Development
Thanks to a team of developers with a strong interest in cybersecurity, Synacktiv can assist you in the creation of security-related software solutions
The development team holds a wide range of knowledge, which allows its members to carry out both "high-level" (eg, development of a security-oriented web front-end) and "low-level" (optimization of a hash algorithm using the SIMD instruction set) engagements.
EXAMPLES OF ENGAGEMENTS
- Development of software in order to fuzz a proprietary industrial protocol
- Development of a network packet parsing module for embedded devices
- Reverse-engineering unmaintained proprietary software to port it to another platform
Tools
Python, full stack, API REST, LLVM, gcc,
Visual Studio, QEMU, Woboq
Visual Studio, QEMU, Woboq
Latest articles
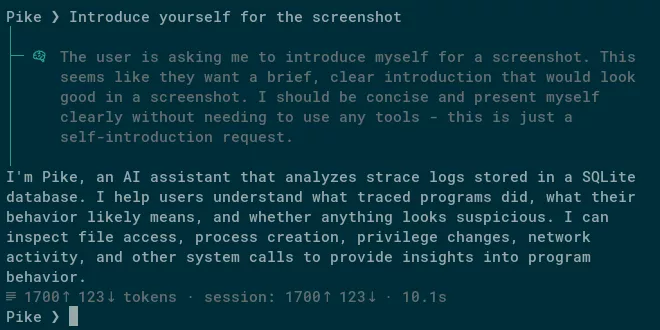
Say hi to Pike!
In this article we will introduce Pike, an experimental LLM agent that generates and analyzes Linux program execution traces. We will show that with its simple architecture paired with a good LLM, Pik
...
mitmproxy for fun and profit: Interception and Analysis of Application Traffic
A solid understanding of the protocols used by applications is a necessary prerequisite when assessing application security. In recent projects, we have had to intercept various types of network traff
...
Creating a "Two-Face" Rust binary on Linux
In this article we will describe a technique to easily create a "Two-Face" Rust binary on Linux: an executable file that runs a harmless program most of the time, but will run a different, hidden code
...